So, at work we use an Active Directory Certificate Services CA for internal certificates, and I had to the So, at work we use an Active Directory Certificate Services CA for internal certificates, and I had to the boxes at work to use a proper certificate for authentication. Here’s the process (mainly so I can remember it in future!) You’ll need OpenSSL installed on your machine, if it’s windows, grab the Win32 OpenSSL binaries.
There’s a few steps:
- Generate the Certificate Signing Request (CSR)
- Generate the Certificate
- Convert the SSL Certificate
- Install the SSL Certificate
Generate the Certificate Signing Request (CSR)
I have a batch file with the following contents called “gencsr.bat”
set OPENSSL_CONF=c:\OpenSSL-Win32\bin\openssl.cfg
c:\openssl-win32\bin\openssl req -out %1.csr -new -newkey rsa:2048 -nodes -keyout %1.key
When I want a CSR for a machine called “hostname” I’d run gencsr.bat hostname
Loading 'screen' into random state - done
Generating a 2048 bit RSA private key
...........................+++
............+++
writing new private key to 'hostname.key'
-----
You are about to be asked to enter information that will be incorporated
into your certificate request.
What you are about to enter is what is called a Distinguished Name or a DN.
There are quite a few fields but you can leave some blank
For some fields there will be a default value,
If you enter '.', the field will be left blank.
-----
Country Name (2 letter code) [AU]:
State or Province Name (full name) [Queensland]:
Locality Name (eg, city) [Brisbane]:
Organization Name (eg, company) [Work Business]:
Organizational Unit Name (eg, section) [Work Company]:
Common Name (e.g. server FQDN or YOUR name) []:hostname
Email Address [[email protected]]:
Please enter the following 'extra' attributes
to be sent with your certificate request
A challenge password []:
An optional company name []:
Generate the Certificate
- Log into your Microsoft Active Directory Certificate Services machine’s web interface (generally https://hostname/certsrv)
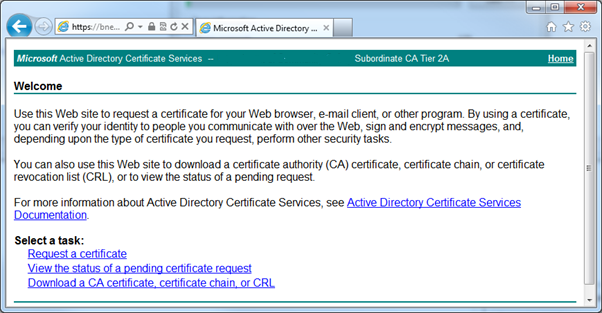
- Click on “Request a certificate”
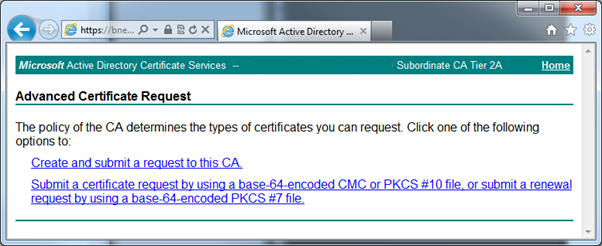
- Submit a certificate request by using a base-64-encoded CMC or PKCS #10 file, or submit a renewal request by using a base-64-encoded PKCS #7 file.
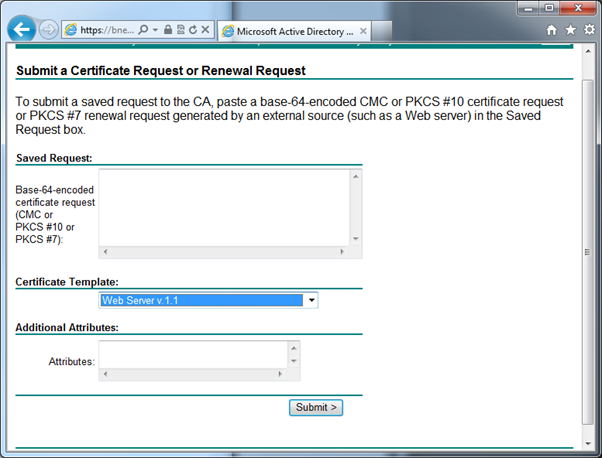
- Copy the contents of the .csr file to the clipboard
- Make sure you set the certificate template to “Web Server v1.1”
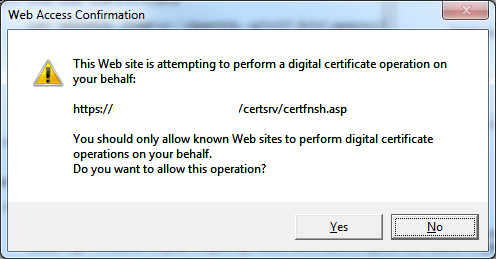
- Click Yes when asked about performing a certificate request.
- Select the “DER Encoded” radio button
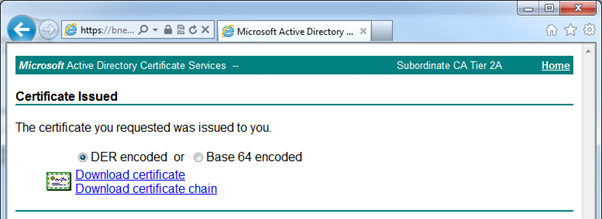
- Download the certificate and the certificate chain, keep the filename’s extension but rename the file to $hostname
- You should have the following files:
- hostname.csr
- hostname.key
- hostname.cer
- hostname.p7b
Convert the SSL certificate
Another batch file, convertp7b2pfx.bat
set OPENSSL_CONF=c:\OpenSSL-Win32\bin\openssl.cfg
rem use this with der-encoded certificates
del .rnd
c:\openssl-win32\bin\openssl x509 -inform der -in %1.cer -out %1.pem
del .rnd
c:\openssl-win32\bin\openssl pkcs12 -export -out %1.pfx -inkey %1.key -in %1.pem
Example (convertp7b2pfx.bat hostname):
> c:\openssl-win32\bin\openssl x509 -inform der -in hostname.cer -out hostname.pem
> del .rnd
Could Not Find .rnd
> c:\openssl-win32\bin\openssl pkcs12 -export -out hostname.pfx -inkey hostname.key -in hostname.pem
Loading 'screen' into random state - done
Enter Export Password:
Verifying - Enter Export Password:
unable to write 'random state'
Install the Certificates
- Make the certs folder:
sudo mkdir -p /opt/splunk/etc/auth/mycerts/
- Upload the .key and the .pem file to the machine in your home directory
- Copy the key/pem file to the right place
sudo cp ~/hostname.key /opt/splunk/etc/auth/mycerts/hostname.key
sudo cp ~/hostname.pem /opt/splunk/etc/auth/mycerts/cacert.pem
web.conf
Edit the web server confiruration:
sudo vi /opt/splunk/etc/system/local/web.conf
Make the file contain the following:
[settings]
enableSplunkWebSSL = 1
privKeyPath = etc/auth/mycerts/hostname.key
caCertPath = etc/auth/mycerts/cacert.pem
Restart splunkweb
sudo /opt/splunk/bin/splunk restart splunkweb
Check the web interface, you should get a valid SSL certificate notice!
Notes
- Yes, the hostname.pem should just be called cacert.cer, but I use these batch files with other windows things so don’t mess with my process!