I was attempting to reconfigure one of our Shark devices this morning and couldn’t use the web interface - RADIUS authentication had been half-configured, setting it to lock things down but with no way to allow me to reconfigure things (even with the admin account) After a little swearing I realised I could SSH into the Shark and reconfigure it that way.
It’s a fairly standard Fedora 10 build, with the Pilot software installed in /opt/local/pilot
The configuration file is /opt/local/pilot/bin/configuration/Pilot.Server.conf
Nano and Vim are installed, so I backed up the file to ~/Pilot.Server.conf.backup and opened it up with an editor. I won’t list the whole file as it’s rather long, but the lines we need to change are here.
# Flow Export Parameters
profilerexport.enabled=False
# Flow Export - Profilers address list
#profilerexport.profilers.address.1=profiler1.riverbed.com
profilerexport.profilers.address.1=
profilerexport.profilers.address.2=
profilerexport.ports.enabled.1=False
profilerexport.ports.enabled.2=False
profilerexport.ports.enabled.3=False
profilerexport.ports.enabled.4=False
Basically, enable profilerexport, set an address and specify the ports you want to monitor (normally, all of them).
# Flow Export Parameters
profilerexport.enabled=True
# Flow Export - Profilers address list
#profilerexport.profilers.address.1=profiler1.riverbed.com
profilerexport.profilers.address.1=[your IP here]
profilerexport.ports.enabled.1=True
profilerexport.ports.enabled.2=True
profilerexport.ports.enabled.3=True
profilerexport.ports.enabled.4=True
Save and close the file, then run “/etc/init.d/pilot restart” without the quotes which will restart the pilot services. I’m not sure, but if you’ve got capture jobs running it might affect capture while doing this.
Once this is done, log out of SSH, you should be done.
To confirm the changes have worked, log back into the web interface and check the status screen. At the bottom there’s the Profiler Export status (you may need to click the little arrow to expand it) If you’ve got data flowing to the shark capture interfaces you should see some flows. It took a few minutes before I saw my first ones, so give it a bit if it doesn’t work straight away.
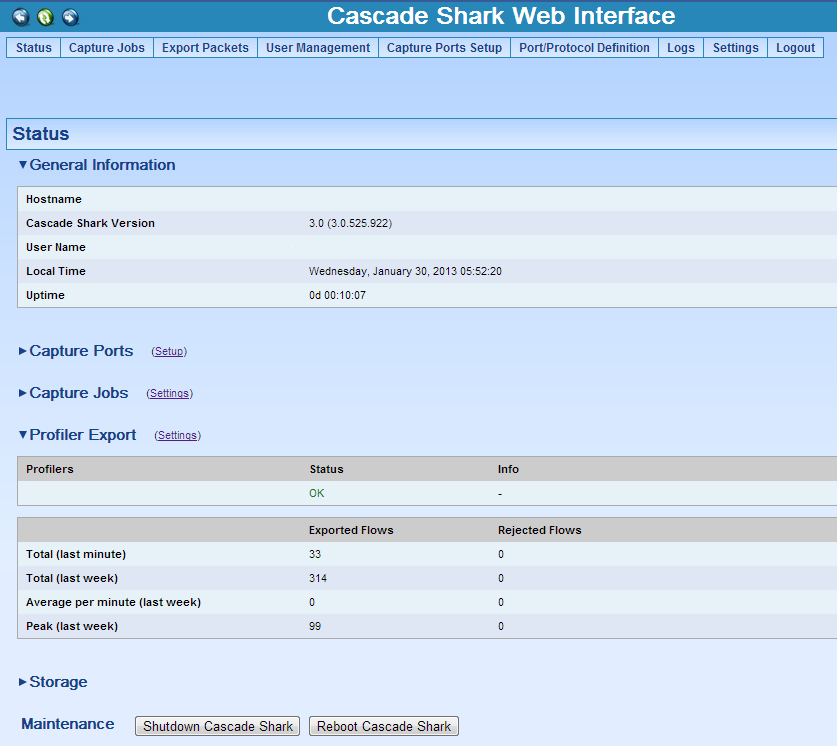 Cascade Shark Web Interface
Cascade Shark Web Interface